Thousands of Stolen Credentials Accessible via Google Search as Cybercriminals Accidentally Make Them Public
A publishing goof by cybercriminals on a WordPress site made files containing stolen passwords indexable by Google and were subsequently publicly available via search.
What initially started as a Xerox scan notification scam intent of stealing victim’s Office 365 credentials became a story of how even the bad guys make mistakes. According to a new report from Check Point, the attackers made a publishing mistake, causing the files containing the stolen passwords to be exposed across dozens of drop-zone servers.
Indexed by Google, the passwords could have been (or possibly were) used by opportunistic hackers if they knew what to search for. According to Check Point, they were able to find dozens of compromised WordPress servers hosting the malicious PHP files that collected and stored the compromised credentials.
Sure, it’s a rather big “if”, but it does go to show you that once a credential is compromised, you have no idea who has access to it, nor how it will be used to further cybercriminal activity.
The way to avoid such situations is to instruct users via Security Awareness Training on how to identify phishing attacks that use brand impersonation (such as Microsoft) to trick victims into giving up credentials in the first place.
Are your user’s passwords…P@ssw0rd?
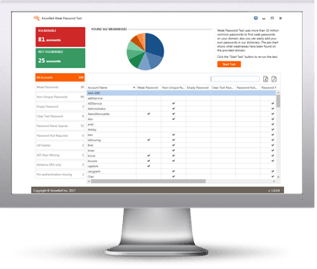
Employees are the weakest link in network security, using weak passwords and falling for phishing and social engineering attacks. KnowBe4’s complimentary Weak Password Test (WPT) checks your Active Directory for several different types of weak password related threats.
 Here’s how it works:
Here’s how it works:
- Reports on the accounts that are affected
- Tests against 10 types of weak password related threats
- Does not show/report on the actual passwords of accounts
- Just download the install and run it
- Results in a few minutes!