[Heads Up] First Omicron Phishing Attack Spotted In The UK
Bleepingcomputer had the scoop. Phishing actors have quickly started to exploit the emergence of the Omicron COVID-19 variant and now use it as a lure in their malicious email campaigns. Threat actors are quick to adjust to the latest trends and hot topics, and increasing people’s fears is an excellent way to cause people to rush to open an email without first thinking it through.
In this case, the Omicron variant is an emerging strain of COVID-19 that has scientists concerned over its high transmissibility and the potential ineffectiveness of existing vaccines against its mutations.
This all makes it an ideal topic for phishing, as even the vaccinated are worried about how Omicron would affect them in the case of an infection. UK’s consumer protection organization ‘Which?’ published two samples of new phishing emails pretending to be from the United Kingdom’s National Health Service (NHS) warning about the new Omicron variant.
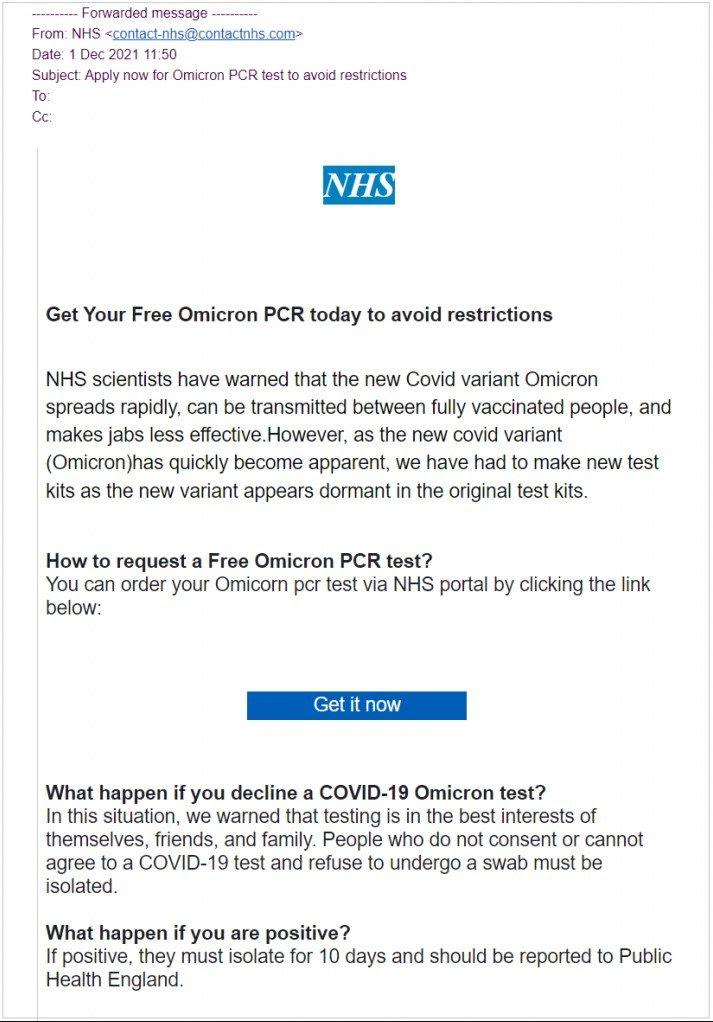
These emails offer recipients a free Omicron PCR test that will allegedly help them “get around restrictions”. To add trust in the emails, the malicious address used for distributing these emails is ‘contact-nhs@nhscontact.com’. If the recipient clicks on the embedded “Get it now” button or taps on the URL in the email body, they are taken to a fake NHS website claiming to offer the “COVID-19 Omicron PCR test.”
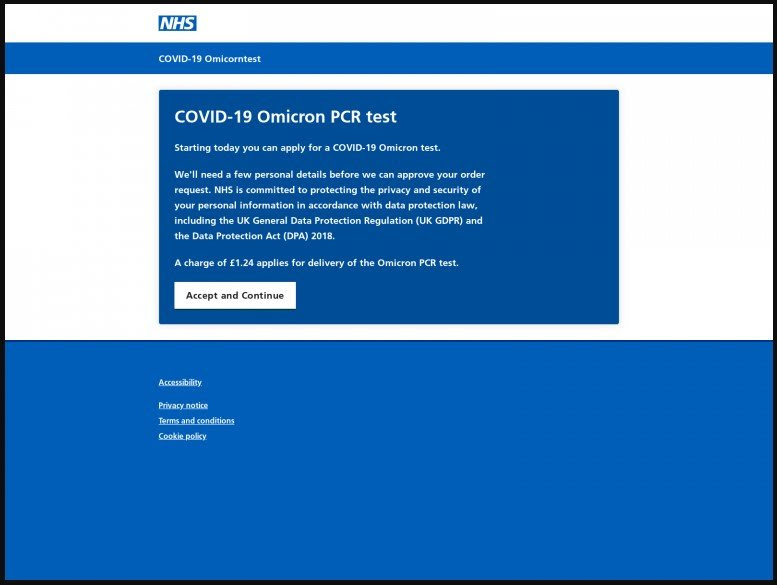
The victims are then directed to enter their full name, date of birth, home address, mobile phone number, and email address. Finally, they are requested to make a payment of £1.24 ($1.65), which is supposed to cover the delivery cost of the test results.
The purpose of this is not to steal the amount itself but the payment details of the victim, like the e-banking credentials or their credit card details. During that step, the victim is also requested to enter their mother’s name, which the actors could use to bypass security questions during a subsequent account takeover attempt.
What to do if you got scammed
If you think you might have entered your details on a fraudulent site, contact your bank immediately and cancel your compromised card/accounts. Monitor your bank accounts closely and review the transactions for any signs of unauthorized payments. If you receive an email that looks suspicious, report it at “report@phishing.gov.uk”. To report smishing texts, forward them to 7726.
Stepping your employees worldwide through new-school security awareness training helps them make smarter security decisions and creates a strong last line of defense.
This is a cross-post with grateful acknowledgment to Bleepingcomputer.