Chameleons Phish, Too
One of the challenges cyber criminals face is that their scams often have a relatively short shelf-life. Once they’ve been used, the gaff is quickly blown, and the scammers hope to realize their gains before most of the potential marks are wise to the scam.
Researchers at Trustwave describe a way in which criminals are trying to get more mileage out of their coding, specifically by developing “chameleon” phishing pages that adapt to their victims’ expectations and so escape exposure. They’re turning up in scams that seek to harvest credentials from unwary victims.
“Recently, we encountered an interesting phishing webpage that caught our interest because it acts like a chameleon by changing and blending its color based on its environment. In addition, the site adapts its background page and logo depending on user input to trick its victims into giving away their email credentials,” the researchers say. “This custom phishing site acts like a chameleon, by changing and blending its images to camouflage itself. There were four noticeable web elements that changed whenever we tested a crafted email address in the browser:
- “The page’s background
- “A blurred logo
- “The title tab
- “The capitalized text of the domain from the email address provider.”
The goal, again, is to give the scam legs, to enable it to stay in use longer. Here’s an example of how it changes for Gmail vs Outlook:
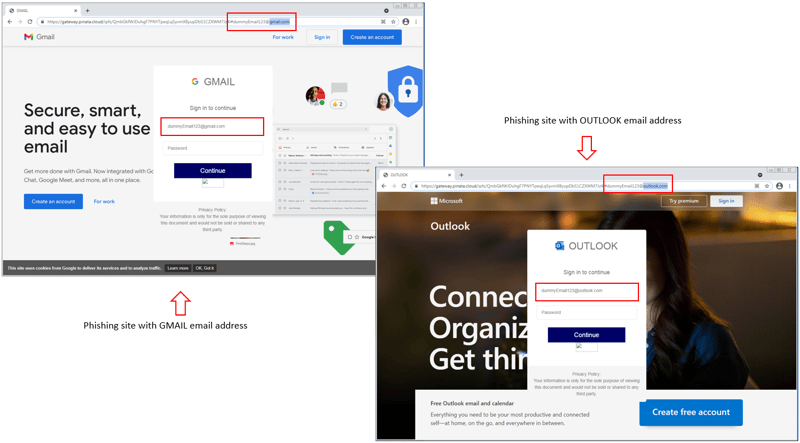 Source: Trustwave
Source: Trustwave
“Phishing webpages are often taken down in a matter of minutes or become unavailable as soon as information security companies detect them as being malicious,” Trustwave explains. “These templated, or so-called chameleon phishing sites, are used repeatedly by malware authors using the clever tricks we just detailed to fool the user into thinking these pages are real. The phishers can easily customize the template and use other domains to host these scripts, allowing attackers to prey on unsuspecting users over and over again.”
Chameleon phishing sites represent another move toward commodifying malware and scamming techniques. New school security awareness training can help users see through the impostures that make their way through an organization’s filters.