There’s No Such Thing as a Free Yeti, Only Social Engineering Tactics
It’s easy to think of the typical online holiday scam as something that affects mostly individuals. Sad, maybe, and unfortunate, but not something that might seriously threaten a business, or another organization.
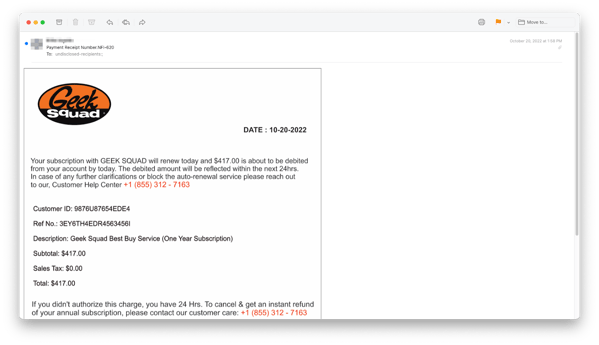
For example, a lot of scams are circulating that offer a free Yeti cooler, or some other attractive bauble, like a Samsung Smart TV, or a snazzy dutch oven by Le Creuset. All you have to do is enter your credit card to cover shipping and handling–fair enough, right? Because after all you’re going to get a swell Yeti. Of course, there is no Yeti, but the scammers have got the marks’ paycard information.
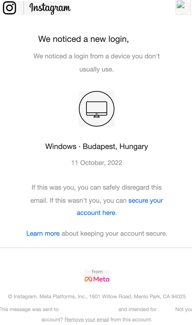
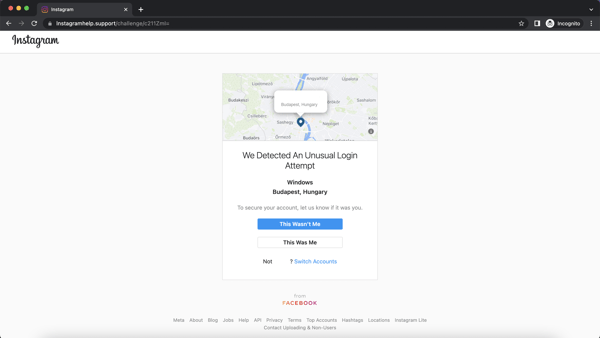
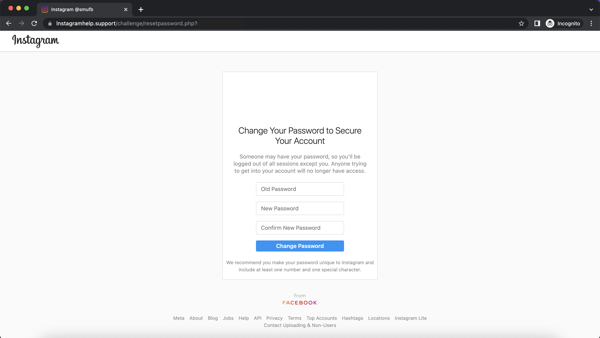
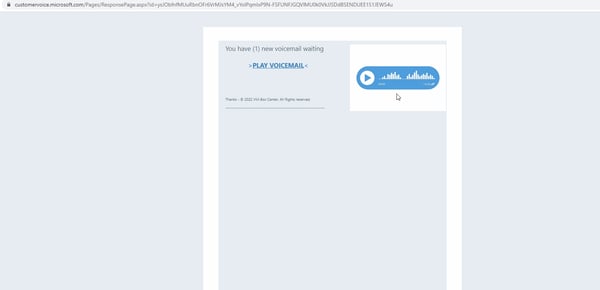
But there are lessons here in social engineering that can be applied by organizations, too. Vox’s Recode explains, “Basically, these scammers are deploying lots of technical tricks to evade scanners and get through spam filters behind the scenes. Those include (but aren’t limited to) routing traffic through a mix of legitimate services, like Amazon Web Services, which is the URL several of the scam emails I’ve received appear to link out to. And, [security researcher Zach] Edwards said, bad actors can identify and block the IP addresses of known scam and spam detection tools, which also helps them bypass those tools.”
There’s also more use of domain hop architecture in spam, helping the scammers hide their tracks and evade security tools. That’s not all. Recode goes on to report that, “Akamai said this year’s campaign also included a novel use of fragment identifiers. You’ll see those as a series of letters and numbers after a hash mark in a URL. They’re typically used to send readers to a specific section of a website, but scammers were using them to instead send victims to completely different websites entirely. And some scam detection services don’t or can’t scan fragment identifiers, which helps them evade detection, according to Katz. That said, Google told Recode that this particular method alone was not enough to bypass its spam filters.”
The upshot of the greater sophistication email spam now exhibits is that the social engineers are working to bypass the technical protections organizations have in place. As is so often the case, the individual user is the last line of defense, and a well-informed, properly skeptical user is to some extent armored against attempts like this. The email might look as if it came from a legitimate sender, the offer might be attractive, but new school security awareness training can help your people understand that, really, there’s no such thing as a free Yeti.
Recent Comments