Karakurt Adds Irritating Phone Calls to its Crimes
The US Cybersecurity and Infrastructure Security Agency (CISA) and its partners have issued a joint alert on Karakurt, a data theft extortion group that harasses victims’ employees, customers, and business partners in order to pressure the victim to pay up.
“Karakurt actors have typically provided screenshots or copies of stolen file directories as proof of stolen data,” the alert says. “Karakurt actors have contacted victims’ employees, business partners, and clients with harassing emails and phone calls to pressure the victims to cooperate. The emails have contained examples of stolen data, such as social security numbers, payment accounts, private company emails, and sensitive business data belonging to employees or clients. Upon payment of ransoms, Karakurt actors have provided some form of proof of deletion of files and, occasionally, a brief statement explaining how the initial intrusion occurred.”
Unlike many similar gangs, Karakurt doesn’t encrypt the stolen data after stealing them, and instead relies solely on threatening to damage the organization and its customers and partners by publishing the data online.
“Karakurt actors have employed a variety of tactics, techniques, and procedures (TTPs), creating significant challenges for defense and mitigation,” the alert says. “Karakurt victims have not reported encryption of compromised machines or files; rather, Karakurt actors have claimed to steal data and threatened to auction it off or release it to the public unless they receive payment of the demanded ransom. Known ransom demands have ranged from $25,000 to $13,000,000 in Bitcoin, with payment deadlines typically set to expire within a week of first contact with the victim.”
CISA notes that “some victims reported Karakurt actors did not maintain the confidentiality of victim information after a ransom was paid.” This should come as no surprise: ransom gangs cannot be counted on to keep their promises.
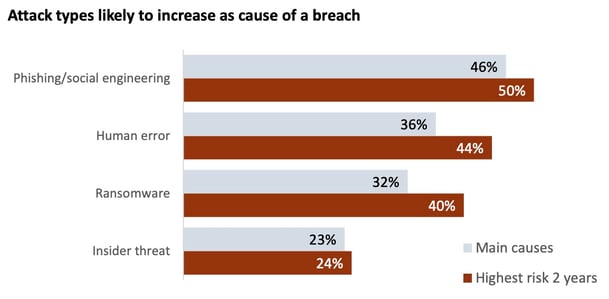
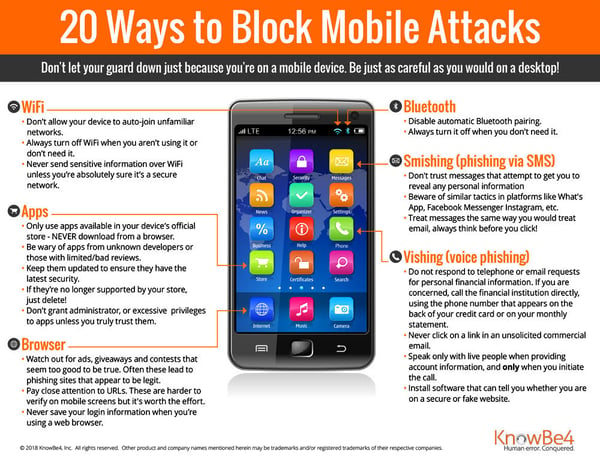
Most ransomware attacks begin with a human mistake, such as an employee falling for a phishing email. New-school security awareness training can give your organization an essential layer of defense by teaching your employees how to recognize social engineering attacks.
Recent Comments