FBI: US Defense Industry Organizations Targeted with USB-Based Ransomware Attacks
Using mailed out “BadUSB” drives as the initial attack vector, cybercriminals are attempting to infiltrate sensitive networks and infect them with BlackMatter or REvil ransomware strains.
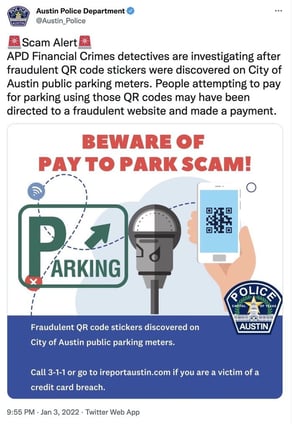
The FBI recently released a notice about cybercriminal group FIN7, according to a Bleeping Computer article, warning defense contractors to be wary of USB drives being sent through the mail. According to the notice, FIN7 is impersonating Amazon and the Department of Health & Human Services (depending on the target victim) in an effort to get them to plug in the USB drive.
The USB drives are ‘BadUSB’ or ‘Bad Beetle USB’ devices with the LilyGO logo, and are commonly available for sale on the Internet. The drives register with the victim computer as a keyboard and include a wealth of hacker tools, including Metasploit, Cobalt Strike, Carbanak malware, the Griffon backdoor, and PowerShell scripts.
The goal of these drives is to infect networks with either BlackMatter or REvil ransomware.
This is a real-world form of targeted attack that uses the same social engineering we commonly see in phishing attacks. Users that undergo continual Security Awareness Training are already aware they should not be plugging in unknown USB drives – especially those sent unsolicited.
These attacks could just as easily be turned into an access for sale attack, given the amount of control hackers have over the compromised endpoint. Be on guard.
Recent Comments