It’s Not Only About the URL
You have to look at the totality of an email to determine whether it is a phishing attack or not.
I’ll admit it, I’m guilty. When I get a phishy-looking email, the first thing I do is hover over the URL to see if it is legitimate-looking or not. And, most phishing emails do contain rogue-looking domains. So much so, that I actually wrote about this here previously and created a one-hour webinar all about how to teach yourself and co-workers how to spot rogue URLs. You can even download our handy Rogue URL PDF handout (shown below) for a quick review or to hand it out to your co-workers.
Analyzing included URLs is a big part of determining if something is malicious or not.
It’s just not the only thing!
The URL Is Not Everything
We all need to look at the totality of the potentially suspicious phishing request to determine if it is malicious or not. URL investigation is a big part of that process, but there are many phishing scenarios where the URLs are indeterminate or even completely, 100%, legitimate. For instance, many phishing emails originate from common, shared domains. For example, many phishing emails come from onmicrosoft.com (0365-hosted domains), gmail.com, sendgrid.net. I’m highly suspicious of sendgrid.net because a lot of phishing emails come from there and then I realized that one of my absolutely favorite computer security portals, Spiceworks, sends all their emails from sendgrid.net. And that’s not a bad thing. Sendgrid.net is a legitimate service used by mostly legitimate people, but because it is widely and publicly available, it is often used by scammers, as are the shared, public domains by Microsoft and Google.
Many times, the phishing emails come from legitimate, private domains. Oftentimes, they are a hijacked domain and the involved link has nothing to do with the brand being or request being impersonated. For example, the rogue URL link says something like waterworks.com/inbox/subscriptions/rogue.jsp, where you can tell that someone’s otherwise legitimate domain and website have been hijacked by a hacker who is using it until the exploit and hole that allowed him/her in is shutdown.
But sometimes, not only is the domain legitimate but it comes from a domain you trust and regularly do business with. Most of the time, the other side you trust has been pwnd and is not being used, unbeknownst to the victim involved, to send spear phishing attacks to people who trust and regularly do business with them. These types of phishes are known as third-party phishing attacks and I wrote about them here. Add to this any time a co-worker has been infected or compromised. The email coming to you could be coming from a close friend.
And sometimes, despite your experience and expertise, looking at the URL just doesn’t solidly indicate whether a suspected phishing attack is definitely a phishing attack.
I found myself relying way too much on URL inspection and my first and often only sign of whether something was malicious or not. So much so that I almost prematurely approved some malicious emails as legit. It happened enough that I was starting to scare myself that one day I would miss one. And even though I knew I was overly reliant on URL inspection, I couldn’t shake the habit at first. I still found myself looking at the URL in a suspected message first and often making the decision then and there.
Drill – Everything But the URL
So, I created a new drill for myself. For months, if I suspected an email or web scenario as being malicious, I refused to look at the URL until the very end of the inspection. I would take my time and see how many other “red flags” of social engineering I could find. Did I see obvious typos? Did I see subject and content mismatches? Did I see email address mismatches? Did the email come in at a strange time? Was the email an unexpected request for something I had never done before? Did the email contain a “stressor” event where it is telling me I had to do something very quickly or there would be consequences? Is it asking me to perform an action that may result in harm? And so on.
My self-imposed drill was a success! In every case of a legit phishing email (or website), I found at least a handful of other clues, that taken in their totality, indicated that what I was dealing with was a malicious phish. Oftentimes, by the time I got to the URL, I had already made my decision. And here is the most important lesson: When I looked at URL last, I was more often able to determine whether an email was malicious or not overall. I didn’t let the URL alone become the primary deciding factor. With my old behavior, using the URL alone or first and primarily, there were definitely times when I wasn’t sure. Using my new strategy, I have successfully determined legitimacy faster and with more accuracy.
If You Still Can’t Confirm Legitimacy
Phishes are ever marching toward more realism. I’m seeing more phishes show up that I can’t as easily determine the legitimacy of, whether or not I’m looking at the URL first. Here’s what I do:
First, if there is a way, I try to confirm the email externally, not using any of the provided information in the email. For example, if it says something has happened to my account that I need to verify, and it links to an account that I actually use, instead of clicking on the URL in the email, I simply go to the legitimate domain, log in, and then see if I get the same warning message. If not, the suspected email was a scam. If the email contains a phone number, especially if I’m told to call it, I go to the Internet, find the real company’s website, look up the phone number there, and call it. If the email claims to be from a department in your company or from a company you trust, call the legitimate phone number you already have on file. Do not call the phone number in the email. Scammers often have fake “switchboards” and operators ready to answer with the right branding.
In moments where I really can’t tell for sure if the email is legitimate or not, I can report it to a trusted colleague. Two sets of eyes are better than one. I’ve got a trusted friend in my company who I trust as much as myself or more to determine legitimacy. Sometimes when I’m in a bind, I send him the email…with a big subject banner indicating what I’m sending him is a suspected phish. And he has really helped me to see clues that I didn’t notice on my own.
At KnowBe4, we are also big believers in the Phish Alert Button. Our Phish Alert Button (PAB) is a free download and works with Microsoft Outlook and Gmail email clients. It installs a “macro” button on the email client’s toolbar that a user can click to report and delete suspected phishing attacks. Admins determine where to collect all suspected phishes ahead of time. It allows an IT security team to investigate individual phishing attempts more quickly and be able to report back to their end users if they reported a real or simulated phishing attempt.
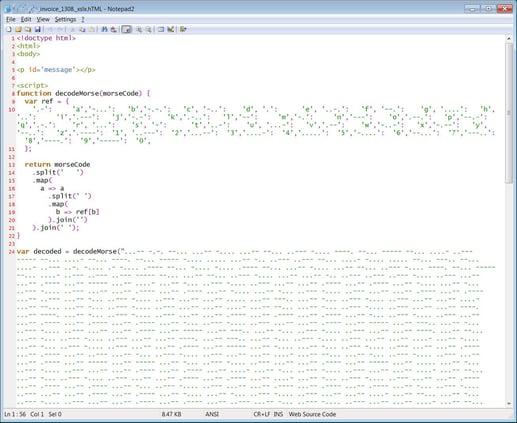
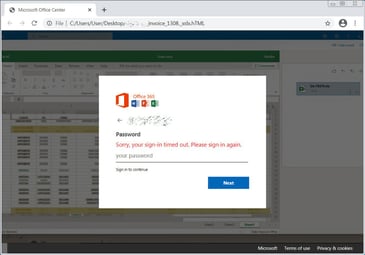
If I have the time, I may send the suspected phishing email to a “throw-away” Hotmail email account I have and then open it up in a safe, isolated, virtual machine. I wrote about how to use Windows 10’s Sandbox feature to do this; although overall, I prefer the professional features offered by VMware, Hyper-V, Parallels, VirtualBox, etc. The Windows 10 Sandbox was convenient, but it just didn’t have enough features and was constantly being corrupted for reasons I don’t know and would not start unless I did a reboot of the host system. If you are interested in forensically examining phishing emails and are inexperienced at doing so, consider watching my webinar. If you don’t know how to forensically examine phishing emails, don’t risk it. Send to a friend instead or don’t do it. It’s all too easy to accidentally click on a link or initiate a malicious JavaScript.
Lastly, when in doubt, chicken out. A few times over the last year, I have received what I’m fairly sure are legitimate emails. Due to nature of my job and writing for nearly 30 years, I receive dozens of emails from complete strangers every day. Many of them are overly familiar, acting as if we are long-time friends, and asking me to click a link to review something for them. Many of those emails are obviously written by English-as-second-language folks, so the sentences and phrasing often looks like what you would see in a real phishing email. I get enough of them that I realize that they are likely legitimate, and I don’t want to not respond and have them think I’m ignoring their email and simply providing poor service. But sometimes, in the end, no matter how hard I try, I don’t know for sure, and when that is the case, I either report it via our PAB button and let the experts determine legitimacy or ignore and delete it. I, and my company, can’t take the risk. When in doubt, chicken out.
We are starting to see more advanced phishes where simply hovering over the included URL doesn’t help you to determine legitimacy or not. You and your co-workers should always look at the totality of the phishing attempt to gauge legitimacy. Don’t rely on the URL alone. All people should be taught how to spot the common “red flags” of social engineering. You can also download and distribute far and wide our “Red Flags of Social Engineering” PDF.
No matter how you learn it, everyone should be educated to understand how to look at the entirety of a potential, suspicious request to determine maliciousness. Here at KnowBe4, we are big believers in security awareness training.
 Source: Bleeping Computer
Source: Bleeping Computer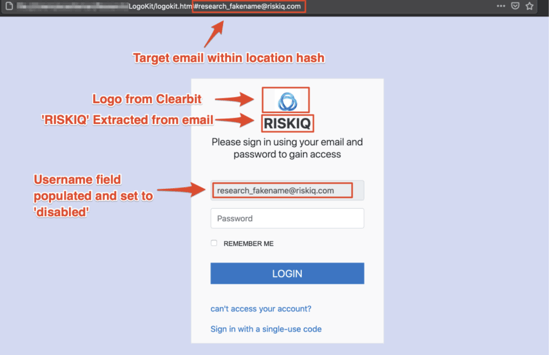
Recent Comments