People often wonder, why are they being phished? Why are they being phished by a hacker in the first place? What does their organization have that some hacker decided they were noteworthy enough to be targeted in the first place?
Targeted vs. Random
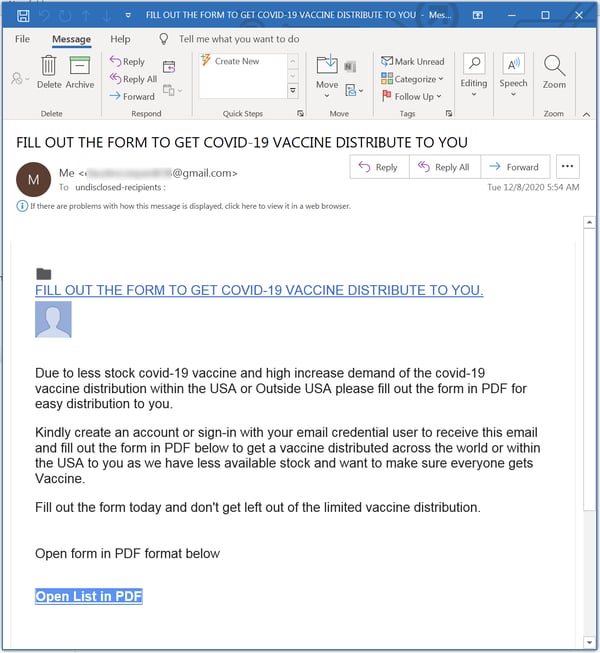
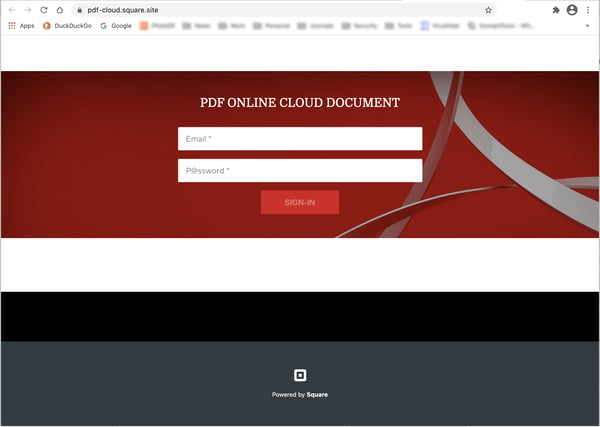
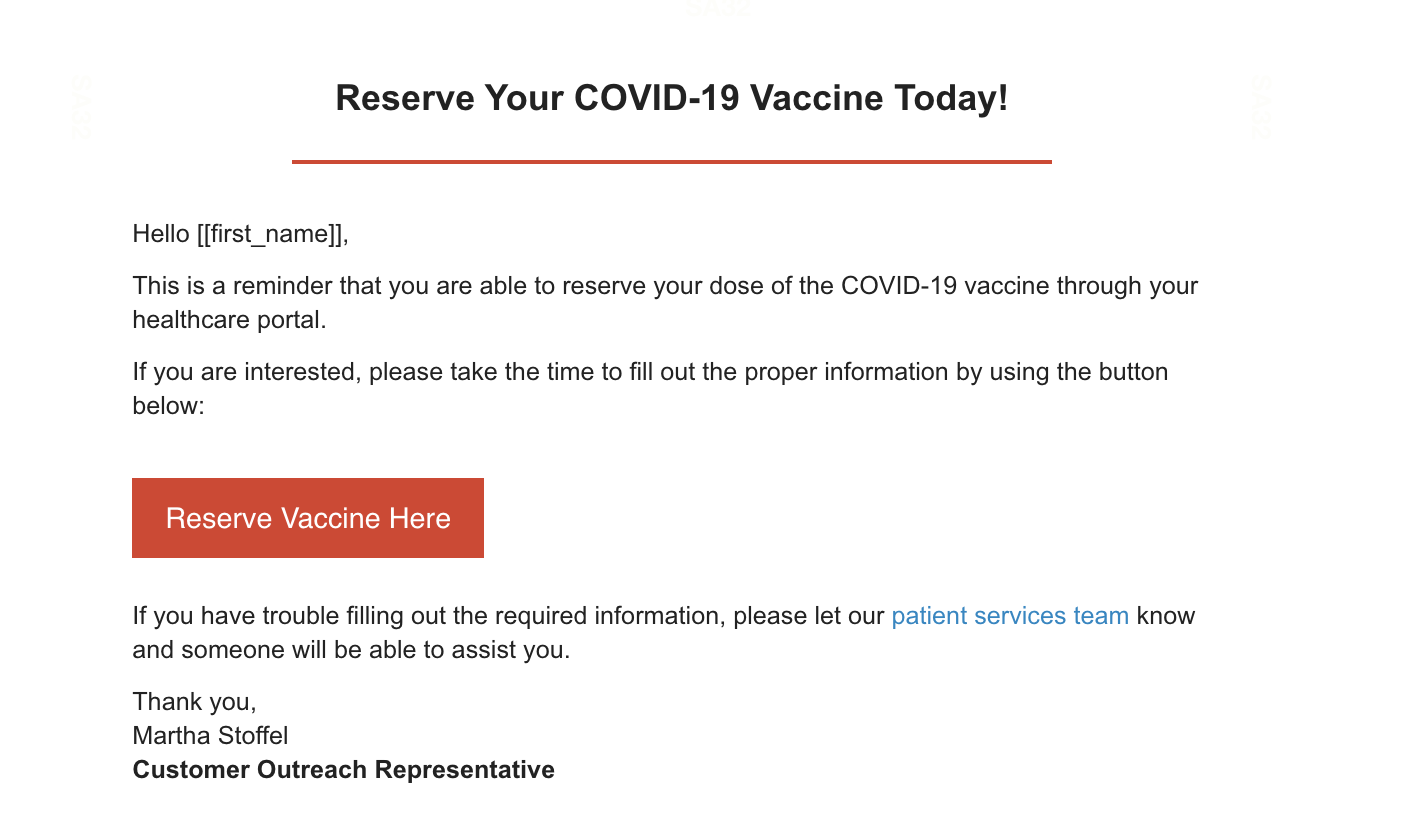
Most organizations are hit by phishing randomly without special targeting. The originating phishing sender had the recipient’s email address, usually from buying or downloading a large bulk list of email addresses or the involved email address was scraped from some other hapless victim who was previously compromised. The hacker and his/her phishing scam didn’t especially pick out a particular victim. They obtained tens of millions or even hundreds of millions of potential victims and their email addresses to send to all of them at the same time and/or over several phishing campaigns. Email addresses from your organization just happened to be on the list. That is how the vast majority of phishing emails end up in an inbox.
The opposite possibility is that your organization was especially targeted, on purpose, by a hacker. For a variety of possible reasons, a hacker decided your company had a reason to be targeted, be it money, intellectual property, nation-state objective, and some other justification. Targeted spear phishing attacks are far less common, but harder to defend against.
Random Phishing Attacks
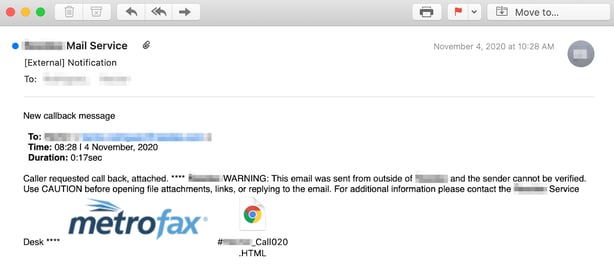
Actually, there is a third, very common, hybrid answer that blends the two main methods. Increasingly, random phishing attacks drop malware which breaks into an organization’s computers and then notifies the hacker of its successful breach. Usually, the initial exploit is accomplished by a malware program designed primarily to get a foothold onto a system or network. It then immediately “dials home” to its “command & control” (C&C) servers, to download the latest, updated, currently undetectable-by-antivirus version of itself. It then downloads and follows any commands left waiting for it by the hacker, if any. The instructions could include telling it to steal data, initiate a ransomware payload, get involved as part of a bigger distributed denial of service (DDoS) attack, or simply to wait.
The initial instructions will often tell the malware to search for all the available passwords and login credentials that can be found on the involved system and upload them to the hacker. Then it will go into a pseudo-hibernating mode and wait for the hacker to send further instructions. They will also get the new IP addresses or domain names for their always moving C&C servers to ensure that one or a few C&C shutdowns by the AV vendors and authorities don’t interrupt their operations.
Many malware programs are inside of systems and networks for up to a year without being detected. They do this by constantly updating to make sure they have the latest versions and remain undetectable by most antivirus programs. Its creator or code will often check Google’s VirusTotal, which runs 70-plus antivirus engines. It’s a good place for hackers to check to see which malware detectors are starting to recognize their programs. If they see AV detection starting to happen, they will re-encrypt or re-obfuscate their malware programs to make the modified malware programs newly “invisible” to the current AV signatures.
It’s very common for hackers today to check their online admin consoles, to which each and every malware bot reports (via the C&C servers). The admin consoles, which reside on yet another C&C server, contain a lot of useful information, including total number of successful infections, country locations, which operating systems and browsers were involved, and the exploited IP addresses and/or domain names. If hackers have the time and desire, they can look over the list of reported domain names. And if they see one that catches their eye for some reason, they can remotely access the compromised device and take a look around. They might find some interesting data to steal or lurk around reading C-level emails to see what they can encrypt or steal to get the most leverage or revenue. At any time in this world, there are likely dozens to hundreds of malware gangs controlling hundreds of thousands to millions of compromised nodes, with the power to do whatever they want whenever they want; limited only by the capability of the software and hardware. It’s a hacker’s dream these days.
Defending Against Cyber Attacks
Targeted attacks are very hard to stop from being successful, especially if the human adversary has nearly unlimited time and resources, like a well-funded hacker gang or nation-state. It is rare that organization will withstand a sustained, focused effort. However, unlike targeted attacks, random and hybrid attacks are many thousands of times more common and can be more easily defended against.
Here’s the possible surprise. All types of attacks, targeted or random, can be defended against in the exact same way. It really doesn’t take any extraordinary defenses. No special gizmos or super expensive solutions are needed. Simply better patching Internet-accessible software and fighting social engineering better is 90% to 99% of the battle ().
Significantly better mitigating those two attack methods will put down most attacks – targeted or otherwise. It just has to be done consistently and more accurately. It requires understanding that these two attack methods are used far more often than any other attack method and then focused on by the defender. The reason most organizations got compromised is because they attempted to do too many things all at once and lost focus on the two things that matter the most. Hackers love it when defenders get distracted.
From a purely defensive point of view, it really doesn’t matter why your organization was targeted by a phishing campaign. It does matter, especially if they are successful. But you implement the exact same preventative, detective, and response controls for both of them.
If you want to learn about everything you can do to prevent social engineering and phishing from being successful (including policies, technical defenses, and education), you can watch the On-Demand Webinar: your Ultimate Guide to Phishing Mitigation.
Recent Comments