FBI Warns of Fraudsters on LinkedIn
The US FBI has warned that scammers on LinkedIn are a “significant threat,” CNBC reports. Sean Ragan, the FBI’s special agent in charge of the San Francisco and Sacramento field offices, told CNBC in an interview that cryptocurrency scams have been particularly widespread recently.
“This type of fraudulent activity is significant, and there are many potential victims, and there are many past and current victims,” Ragan said. “So the criminals, that’s how they make money, that’s what they focus their time and attention on,” Ragan said. “And they are always thinking about different ways to victimize people, victimize companies. And they spend their time doing their homework, defining their goals and their strategies, and their tools and tactics that they use.”
LinkedIn stated in a blog post last week, “While our defenses catch the vast majority of abusive activity, our members can also help keep LinkedIn safe, trusted, and professional. If you do encounter any content on our platform you believe could be a scam, be sure to report it so that our team can take action quickly. This includes anyone who asks you for any personal information, including your LinkedIn account credentials, financial account information, or other sensitive personal data. We also encourage you to only connect with people you know and trust. If you’d like to keep up with someone you don’t know but that publishes content that is relevant to you, we encourage you to follow them instead.”
LinkedIn offered the following recommendations in a blog post:
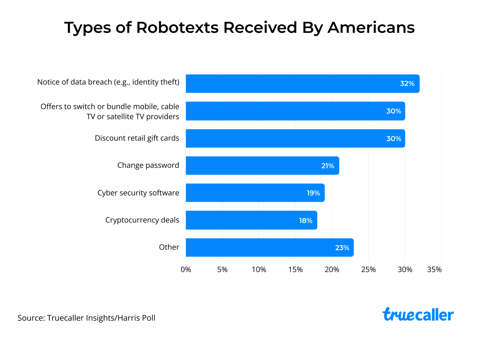
- “People asking you for money who you don’t know in person. This can include people asking you to send them money, cryptocurrency, or gift cards to receive a loan, prize, or other winnings.
- “Job postings that sound too good to be true or that ask you to pay anything upfront. These opportunities can include mystery shopper, company impersonator, or personal assistant posts.
- “Romantic messages or gestures, which are not appropriate on our platform – can be indicators of a potential fraud attempt. This can include people using fake accounts in order to develop a personal relationship with the intent of encouraging financial requests.”
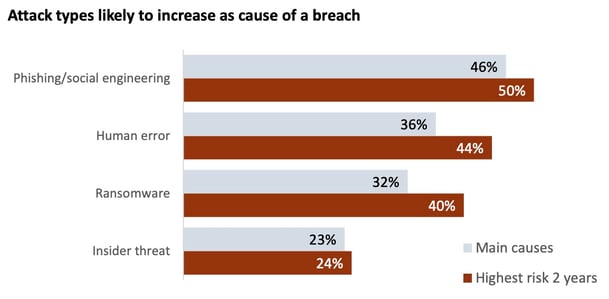
New-school security awareness training can teach your employees to follow security best practices so they can avoid falling for social engineering attacks.
Recent Comments