Cryptocurrency Scam Profits Jump 81% in 2021 to $7.7 Billion
Despite a massive drop in crypto scams in 2020 due to the pandemic, a new report highlights the massive growth in crypto scams… and the profitable results they’re yielding.
I recently covered a new scam promoting the faux “presale” of Amazon tokens – this scam is one of countless others all taking a similar approach. The main motive is to gain interest in an either bogus token that doesn’t exist (as in the Amazon scam) or build interest in a new crypto and then ditch the project after victims invest. These scams are referred to as “rug pull” scams.
According to crypto analysis firm Chainalysis’ 2022 Crypto Crime Report, it’s these “Rug Pull” scams that account for the massive uptick in crypto scams in 2021. According to the report, the lion’s share of the growth in 2021 profits came from Rug Pulls.
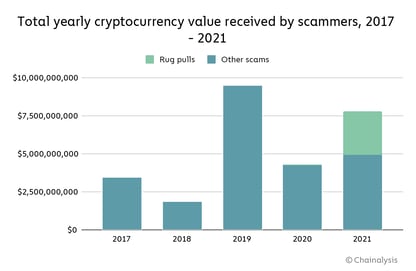
Source: Chainalysis
In addition to Rug Pulls, investment scams – scams in which victims are promised high investment returns in exchange for putting up crypto assets they will never see again are also on the rise. According to the Chainalysis data, the number of investment scams rose in 2021 by over 60%.
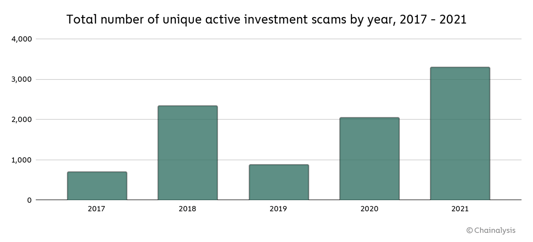
Source: Chainalysis
Most investment scams last an average of just 70 days (that’s down from 192 in 2020). Even the U.S. Securities and Exchange Commission recently put out a notice about the danger of these investment scams.
Novice and professional investors alike should be wary of such scams as there are ways to make much higher investment returns legitimately than, say, the stock market, but the investor’s desire to make a quick buck because they’re “in early” on a new crypto, etc. likely isn’t going to pan out the way they plan.

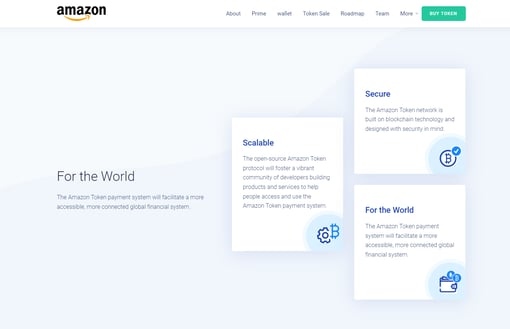
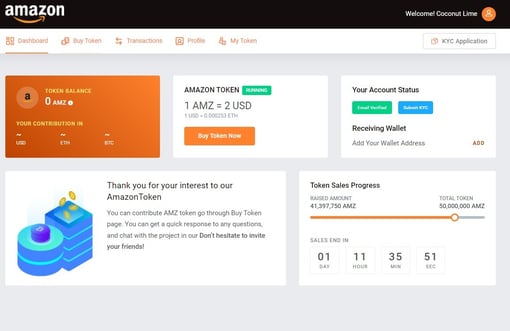
 Here’s how it’s done:
Here’s how it’s done:
Recent Comments