Celebrity Hacks and the Frenzy of Renown
Avast offers a look at incidents in which celebrities have been the victim of social engineering attacks. The firm notes that while celebrities are higher profile targets, attackers use the same tactics against them that work against everyone else.
“Most of the time, celebrities get hacked the same ways anyone else does,” Avast says. “They use weak passwords, fall for social engineering tricks, or suffer from data leaks when larger organizations holding their data are breached.”
In some cases, however, celebrities are victims of attacks they have no control over, such as the breach of law firm Grubman Shire Meiselas & Sacks.
“Celebrity law firm Grubman Shire Meiselas & Sacks, which counts among its clients such A-listers as Madonna, Lil Nas X, Robert De Niro, and LeBron James, recently found itself on the receiving end of a massive hack,” Avast says. “In May 2020, the noted hacking collective REvil — also known as Sodinokibi and one of the world’s most dangerous hacking groups — claimed to have stolen over 750 GB of contracts, emails, NDAs, and other sensitive data. REvil (short for Ransomware Evil) initially demanded a ransom of $21 million, then doubled it. Refusing to pay, the law firm instead turned to the FBI for help.”
In this case, however, the stolen information fortunately wasn’t as sensitive as the hackers made it out to be.
Avast offers the following advice if your accounts or devices are hacked:
- “Isolate the hacked device: Unplug any Ethernet cables and disable Wi-Fi on the hacked device. This will prevent any malware from spreading or sending data back to the hacker.
- “Change your passwords: Using an unhacked device, create long, hard-to-guess, and unique passwords for all your accounts and devices — we recommend using passphrases. Strong passwords will lock hackers out of your accounts and prevent them from using old passwords to log back in.
- “Report the hack and recover your accounts: Most online services, such as Gmail or Facebook, have specific procedures in place for reporting hacks. Follow these procedures for each hacked account to regain control.”
New-school security awareness training can enable your employees to follow security best practices so they can avoid falling for these attacks.
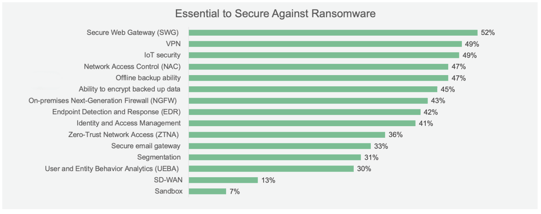 Source: Fortinet
Source: Fortinet
Recent Comments