$148 Million Lost to Gift Card Scams in 2021 (So Far)
A US Federal Trade Commission (FTC) data spotlight has found that people in the US lost $148 million to gift-card-related scams in the first nine months of 2021. The spotlight also found that median reported losses from these scams increased from $700 to $1,000 throughout the same period.
“Scammers favor gift cards because they are easy for people to find and buy, and they have fewer protections for buyers compared to some other payment options,” the spotlight explains. “Scammers can get quick cash, the transaction is largely irreversible, and they can remain anonymous.”
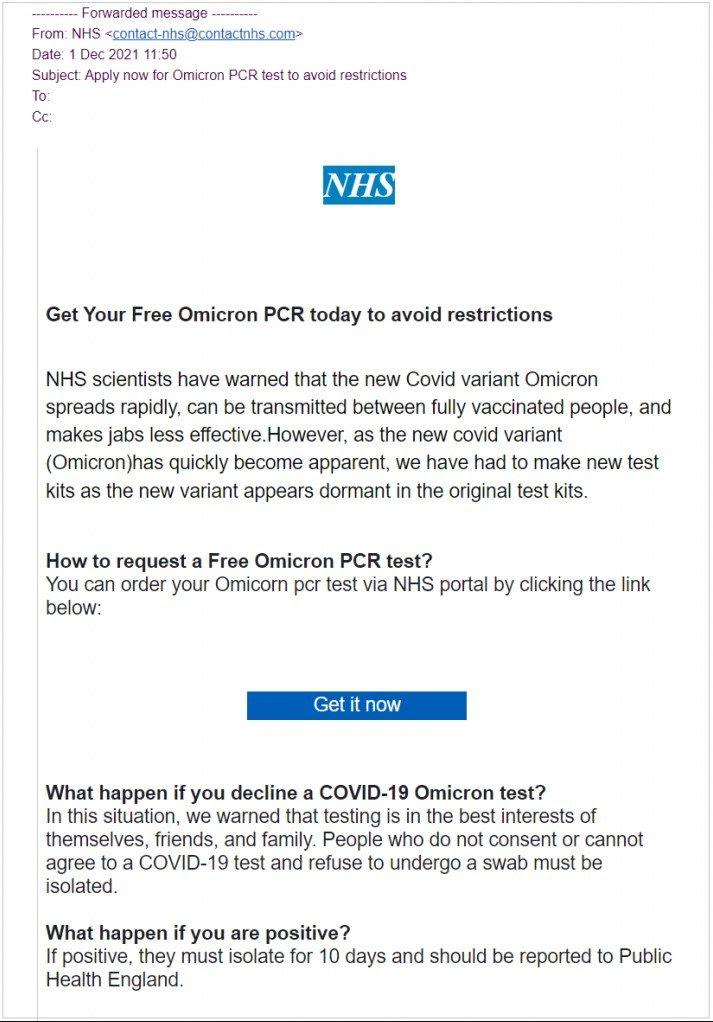
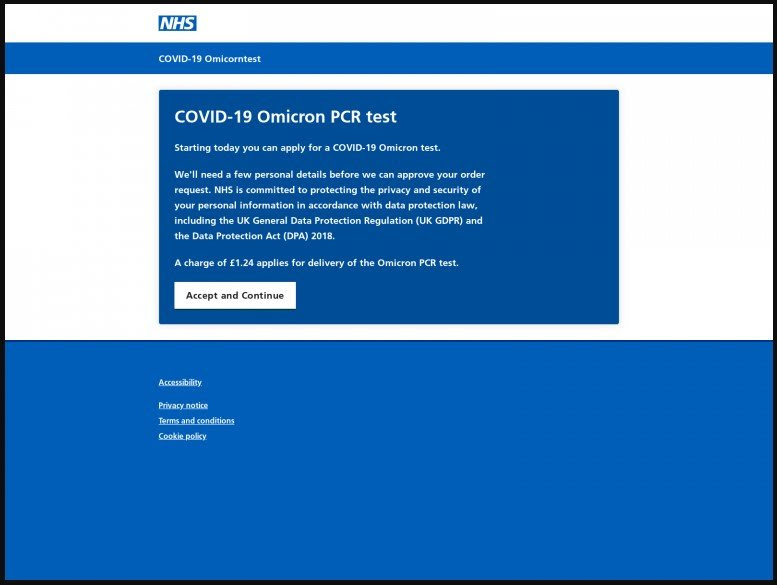
The spotlight explains how scammers use social engineering to trick people into spending hundreds or thousands of dollars on gift cards.
“According to reports received by the FTC, scams demanding gift cards most often start with a phone call from someone impersonating a well-known business or government authority,” the report says. “Many people report that a scammer posing as Amazon or Apple told them to send pictures of the numbers on gift cards to fix a supposed security problem with their account. Sometimes they call those numbers ‘security codes.’ But the only thing the numbers are good for is taking the money on the card. Other people report that a scammer claiming to be the Social Security Administration said their bank accounts would be frozen as part of an investigation. They’re told to buy gift cards to avoid arrest or to secure access to their money. Reports also show that scammers asking for gift cards pretend to be a love interest, employer, sweepstakes or lottery company, or family member in trouble.”
The FTC also notes that scammers appear to favor Target gift cards.
“In the first nine months of 2021, over twice as much money was reported lost on Target gift cards than any other brand,” the FTC says. “Google Play gift cards were next, followed by Apple, eBay, and Walmart cards. Scammers also tell people where to buy the gift cards. In the first nine months of 2021, people who reported losing money buying gift cards mentioned Target stores more than other retailers. Reports suggest that Walmart, Best Buy, CVS, and Walgreens stores are also popular with scammers.”
New-school security awareness training can enable your employees to recognize social engineering tactics.
Recent Comments