One Out of 10 Threats Still Make It All the Way to the Endpoint
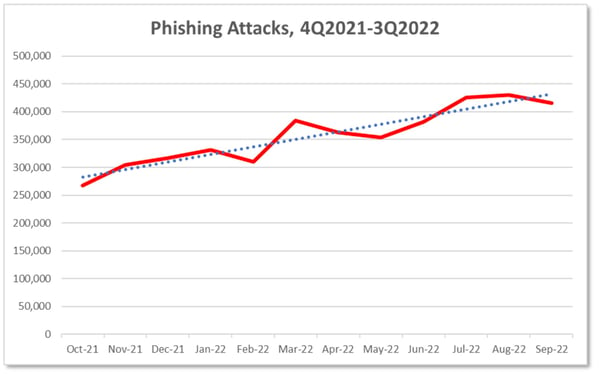
Despite good intentions, layered security measures, and efficacy claims by security solution vendors, new data shows that email-based threats are still getting all the way to the Inbox.
Given all that your organization has in place to stop threats from entering into your environment, you’d like to think it all gets stopped. Your security vendors certainly tell you that their solution stops some very high percentage of attacks – likely in the 99-point-something range. And the layered defense you’ve implemented is designed to address attacks from a number of directions, giving you a heightened chance of stopping an attack before it does any damage.
But new data from Acronis in their End-of-Year Cyberthreats Report shows that 11.7% of all attacks still make it to the endpoint. This is a nearly 11% increase from the previous quarter – meaning threat actors are getting better at avoiding detection and obfuscating the malicious nature of their emails.
Part of this “success” may be due to the short lifespan of a given piece of malware – according to the report (emphasis is mine):
The average lifetime of malware samples in November 2022 was 1.7 days, after which a threat would disappear and never be seen again. In Q2 2022, this figure was at 2.3 days, showing that malware is even more short-lived today as attackers use automation to create new and personalized malware with a frequency that overwhelms traditional signature-based detection. Seventy-four percent of the samples observed were seen only once across our customer base.
With this newfound data, it should be obvious that you should expect that malicious emails are going to find their way past your security solutions, making it absolutely necessary for your users to play a part in organizational security by being vigilant when interacting with email and the web – something taught with continual Security Awareness Training.
Recent Comments