[HEADS UP] FBI Warns of Tech Support Scams That Impersonate Payment Portals for Fake Refunds
In the latest FBI warning, cybercriminals are now impersonating financial institutions’ refund payment portals. This effort is to contain victims’ personal information with legitimacy.
These bad actors are using social engineering to trick victims into giving them access to their computer by impersonating representatives of technical repair services. In details from the FBI’s public service announcement lists the following, “Within the body of the email, the scammers will indicate the specific service to be renewed with a price commonly in the range of $300 to $500 USD, provoking a sense of urgency in the victims to contact them and provide information for a refund.”
Although tech support scams are very common, the FBI did note that as recent as last month scammers are using scripts that portray a refund payment portal when it is actually a malicious site.
BleepingComputer found samples of these scripts below pretending to be various financial institutions:
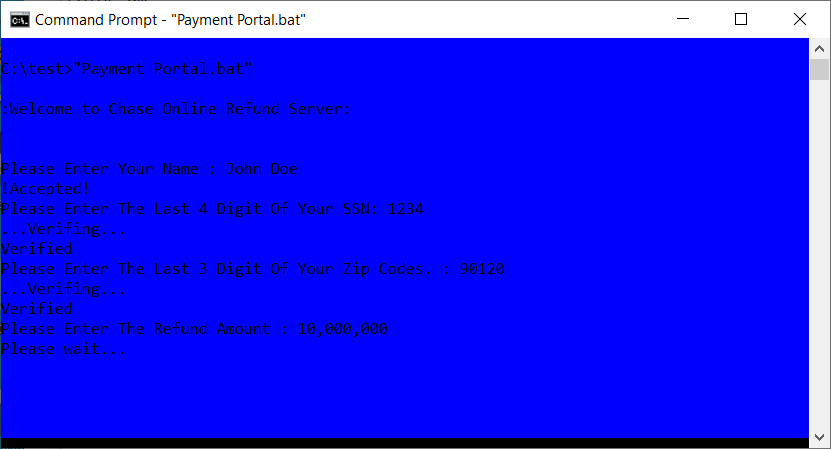
Source: BleepingComputer
The FBI is encouraging any potential victims to not grant remote access at all to any unknown person and to not send wire transfers at all through online or phone communications. Frequent new-school security awareness training is highly encouraged for your users to avoid these types of tech support scams in their day-to-day operations.
Recent Comments