I was fortunate enough to write Wiley’s Hacking Multifactor Authentication. It’s nearly 600-pages dedicated to showing attacks against various multi-factor authentication (MFA) solutions and how to prevent them. It picks MFA winners and losers and contains a framework and checklist to help anyone pick the right MFA solution for themselves and their organization.
I’ve been lucky enough to be hired to hack many different MFA solutions over my over 30-year computer security career. I’ve created fake fingerprints, taken pictures of irises, and hacked a ton of physical MFA devices. I once hacked over 20 different fingerprint readers as part of one project alone. As part of the book, I reviewed dozens of different MFA solutions and looked at over 130 products (they are listed in the Appendix). To be clear, I didn’t physically hack 130 different MFA solutions, but I did review what they did, how they worked, and was able to rely on my 30 years of experience in determining whether I could likely hack them or not. Along the way, I’ve learned a few key lessons, including:
You Can’t Use MFA in Most Places
Whenever I read that passwords are going away and will soon to be replaced by something else, usually MFA, I want to laugh. In what world? Passwords work with likely 99% of most authentication-protected websites. I’m not sure what percentage really. I’m just making up the 99% figure. But passwords have been around with us and used with different websites, services, and applications for decades. Passwords are easily the most commonly accepted form of authentication. Kids as young as two have no problem using a login name and password. Even most websites and services that accept MFA still also accept passwords, used by themselves, as valid authentication.
The converse is not true. In comparison, MFA is hardly accepted anywhere. Again, I don’t know the real percentages, but MFA likely doesn’t work on 1% of the world’s websites, services, and applications. The average person has over 170 websites/services they login to, plus many more applications. Most of those don’t accept MFA. Some do. Most don’t.
What I’ve learned is that when you go to pick an MFA solution that’s right for you or your organization, step one is to figure out what websites/services and applications you want to protect by MFA, and then figure out which MFA solutions can actually protect those sites and applications. Unless you are unusually homogenous for an organization (say for example, run nothing but Google applications), you’ll have a hard time finding a single MFA solution that protects everything you want protected. Usually, you’ll end up with one of three answers to solve the misalignment:
- Select a smaller set of things you want to protect with a single MFA solution
- Select multiple MFA solutions, each protecting a subset of what you want to protect
- Select a single-sign-on (SSO) solution that can protect everything you want to protect, which puts an MFA login shell around them
In most cases, you’ll end up selecting two or more of these answers. There just isn’t a single MFA solution that covers even a moderate percentage of the world. Pick the most popular solutions (e.g., Google Authenticator, FIDO, RSASecurID, Yubico, Microsoft Authenticator, Okta, Duo, WatchGuard, etc., and you’ll not find any of them that work with much of the Internet.
They may they cover thousands or even hundreds of thousands of websites and services, but the Internet is a very big place with hundreds of millions of web sites and there are hundreds of millions of applications. Unless you code every application and site yourself or buy them from one vendor, you’re going to be making trade-offs.
The reality today is that most of us are ending up with one or more MFA solutions plus a bunch of passwords. Most of us have one MFA solution that works with some of the stuff we have at work, others that work with our personal sites and services (e.g. social media, banking, stock accounts, etc.). And many dozens of passwords. Welcome to the real world! Every time I hear someone say that passwords are going away, I want to buy stock in a password manager vendor.
All Can Be Hacked
A lot of attendees to my 12 Ways to Hack MFA webinars are shocked when I say all MFA solutions, even the ones they love the best, can be hacked! I’m surprised at their surprise reactions. Nothing is unhackable. Nothing. And that includes any MFA solution.
There are certainly some solutions which are less hackable than others, but I can hack any MFA solution at least a handful of different ways, many of which have nothing to do with the vendor or their implementation. I can attack things, like DNS, or use an electron microscope to find secret encryption keys stored on memory chips, that the vendor has no control over. I can hack most MFA solutions over five ways and hack many of them over a dozen ways. If you want the specifics, read my book.
With that said, I did write an earlier, free 41-page ebook. I think it only has 18 ways I can hack MFA (my book has over 50), but they are most of the major ways. We also made a cool, free Multifactor Authentication Security Assessment tool. It asks you a dozen or so questions to determine how your MFA solution works and then it spits out a big report that explains all the ways my brain could hack your submitted MFA solution. This tool was written when I only knew a few dozen ways (and not over 50 like I know today), but it will give you a very good sense of what is possible, hacking-wise, against your submitted MFA solution. But to be clear, every MFA solution can be hacked, and that is to be expected.
KnowBe4 has plenty of other related free content and resources, including KnowBe4’s Multifactor Authentication web portal at: https://www.knowbe4.com/how-to-hack-multi-factor-authentication.
Some MFA Solutions Are Less Hackable Than Others
With that said, some MFA solutions are less hackable than others. Most of your very popular solutions, some of which I mentioned above, are well-designed and constructed. The vendor’s attention to detail and focus make their solutions better than some solution you’ve never heard of. They have the money to hire the best people and teams to design good solutions.
Unfortunately, the vast majority of MFA offerings are fly-by-night offerings, created by one to a few people, with almost no financial support. Most solutions are looking for their first major customer. Many of these smaller offerings are created by very smart people with the best of intentions, but without deep pockets that a steady, incoming, revenue stream provides, it can be hard for them to provide a great all-around solution. With little money, usually one or more things has to suffer.
But more than popularity and size determines the robustness of security. Most of the time, the overall design, dependences, and framework determines what can and can’t be done against a particular solution. After reviewing over 130 solutions, here are the types of solutions and features that I thought provided adequate to above average security protection:
- FIDO2-compliant MFA devices
- Push-based phone applications
- Open Authentication (OATH) solutions
- Solutions using Dynamic Symmetric Key Provisioning Protocol (DSKPP), aka RFC 6063 (tools.ietf.org/html/rfc6063)
And solutions and features I did not like so much:
- Any SMS-based solution
- Biometrics, especially single-factor biometrics
- Single-factor authentication tokens
- Solutions with unknown or proprietary cryptography
- Solutions with personal knowledge-based questions for recovery
- Connect-the-dot type solutions
- Solutions coded by developers without security design lifecycle (SDL) concepts
I’m sure I’ve offended half the vendors reading this article. This is just my opinion from 33 years of looking at and hacking MFA solutions. Your mileage will vary. And most of the time, even a “weaker” MFA solution can provide benefits over simple login name/password solutions. But not even all the time in those instances. There are solutions that I think are worse than just login name/password solutions, and that includes 1FA (single factor) devices that you simply plug into your computer (lose it and the finder essentially gets your identity). I’m especially not a big fan of biometrics used in remote office scenarios. That’s just asking for trouble.
Over-Engineered Solutions
There are also plenty of MFA solutions which, in an attempt to be very secure, go overboard. There is this false impression that many MFA developers have that the world doesn’t have secure-enough MFA solutions, and that is just what the world needs and wants – a four- to 10-factor MFA solution. I have reviewed many MFA solutions that have four or more factors and require people to do manual code lookups or even solve a math problem to login. I’ve got news for those developers – the world will not be beating a path to your door. MFA users want the least amount of “user friction” to be secure and do their job, and a four- or more factor solution is just overkill. Users don’t want a four-factor solution to login to work, much less go on Amazon.
Education is Crucial
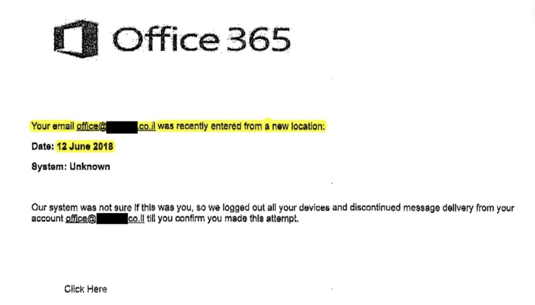
Every MFA solution can be hacked, some by a regular-looking phishing email. But most administrators and users don’t understand that fact. Many believe that using MFA makes them far less likely to be successfully hacked. And that is true for many hacking scenarios. For example, if a hacker sends you a phishing email asking for your password and you’re using MFA and don’t have a password, well obviously, that scam isn’t going to work.
But MFA only prevents certain types of authentication hacking scenarios and not even all authentication hacking. It certainly doesn’t stop the vast majority of hacking attacks. More specifically, if an attacker learns that you are using MFA, he/she can construct or use attacks that are likely to be successful against them if the user isn’t aware of the risks.
That’s why it is crucial that all involved (e.g., management, admin, users, help desk, etc.) be educated about the types of attacks and what could be successful against their particular MFA solution. An informed user is a safer user. Users who are unaware of the risks are more likely to fall for those types of scams and hacks. We let end users know about the risks of and types of attacks against their password. We just have to do the same thing, even if they are using MFA. MFA doesn’t change the need for users to be aware of the threats and risks they face, no matter how they authenticate.
Recent Comments