Learn to Combat These Three Cybersecurity Monsters This Halloween and Beyond
It’s that time of year again. The air feels a bit crisper; the days are a bit shorter; and children around the world prepare to go trick or treating. Even as an adult, Halloween is probably my favorite holiday. I love seeing and thinking about monsters and things that lurk in the shadows… maybe – just maybe – that’s what drew me to a career in cybersecurity.
As we ponder the horrors of the night, I can’t help but draw a few comparisons between current cyber threats and the monsters we all know and love. Here are three critical cybersecurity monsters to be on the hunt for this Halloween and beyond.
Vampires:
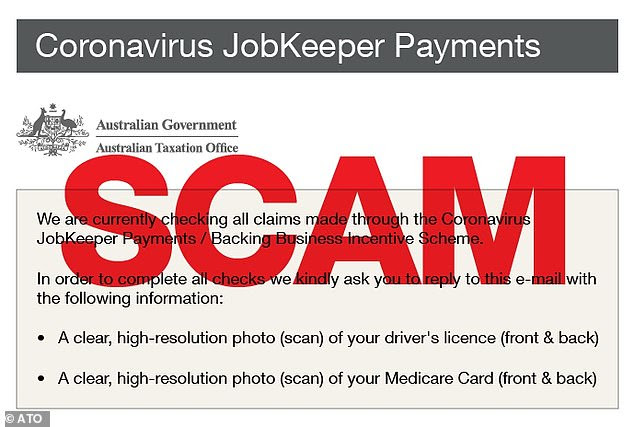
Our first category of monster is the vampire—the cybersecurity bloodsucker. No, not the vendor community. I’m referring to cybercriminals who launch phishing and social engineering attacks.
Phishing and social engineering attacks peel back the thin veneer of control we like to believe we have over our actions. Like a vampire wielding hypnotic control over a soon-to-be victim, social engineers know just how to exploit our very human nature against us. And – before we know it – we’ve fallen victim to that dark power. We’ve clicked a malicious link, entered our login credentials into a fake website, downloaded a malicious attachment, or handed over information that should have been protected. Vampires are masters at stripping away a victim’s self-control so they can sink their teeth into an organization’s lifeblood – it’s data.
Defenders tip: Vampires hate the light, are driven back by symbols of protection, and can be killed by a stake to the heart. Protect your employees and organization by shining a light on social engineering schemes. Talk about current scams and train your employees to battle vampires. Teach them to fight off vampiric attacks by sending them frequent simulated phishing tests. This gives your employees a chance to learn how to slay the vampires by reporting suspected phishing emails… a stake to the heart!
Give users an easy way to report: Get Your Free Phish Alert Button >>
Werewolves:
The next category of monster in our cybersecurity horror safari is the werewolf. Cybersecurity werewolves are negligent or malicious employees.
This is the classic “insider threat;” employees who blend in with all their coworkers most of the time, but can transform into serious threats under the right conditions. These employees may have been bitten by dark outside forces ; they transform into threats when the moon calls. These vicious werewolves savage organizational data, ransack systems, and leave destruction in their wake.
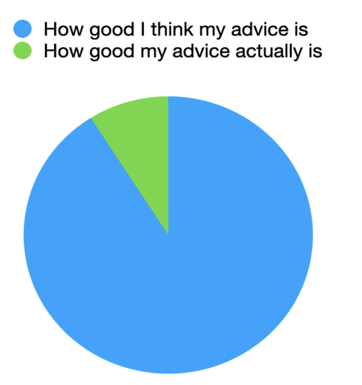
More frequently, however, cybersecurity werewolves are truly mild-mannered employees who haven’t been overtly tainted by dark forces. But their transformation happens when they are under extreme stress, in a hurry, or are clowning around. Even though negligent werewolves may have somewhat innocent motives, it’s important to realize that their effects are still devastating. And one scratch from even these mild-mannered werewolves can infect your employee population.
Defenders tip: Werewolves can be hard to spot since they are usually only in their human form. However, you may be able to detect potential werewolves through blood tests; well… not really. In this case, you conduct “blood testing” through frequent background checks for employees in key areas. Also consider investing in and deploying employee monitoring software to the extent permitted by local regulations. And what about the more innocent, negligent werewolves? Train them constantly so that they are more likely to reflect the behaviors you want and are more likely to stay loyal.
Browse the world’s largest library of security awareness training content: Start Your Preview Now >>
Zombies:
And what survey of monster madness would be complete without a horde of zombies? Zombies are fascinating because they are lifeless and yet slog along. They represent damage, decay, corruption, and a festering of what was once pure. They rampage, kill, and feast on… brains.
Yep – you guessed it – the cybersecurity equivalent of a zombie infestation is today’s plague of disinformation, misinformation, and fake news. Disinformation is the intentional injection of corruption (falsehoods) into the world. Mad scientist disinformation agents want to infect the general population with a scourge of corruption. And they want their initial zombie population to scratch, bite, and otherwise ravage others; allowing the corruption to spread in the form of misinformation (the unknowing/unintentional spread of disinformation). Zombie plagues tend to quickly spread well beyond the confounds of any border or boundary. And, before you know it, there is a vast army of zombies as far as the eye can see; moving slowly and somehow shockingly fast at the same time—like a horde of sickening stop-motion marionettes. They want our brains.
Defenders tip: It’s important to remember that zombies are victims. They may be snarling at us, wanting to infect us, and eat our brains. But that’s only because they were infected by others spreading the disinformation/misinformation virus. The best thing you can do is to remain uninfected and fight for a vaccine. We combat falsehoods with truth. And we bring empathy and compassion to this very human problem. When’s the last time you had a real conversation with a zombie?
Stay informed: Watch the Global Disinformation webinar series >>
Conclusion:
Let’s face it. The world is a scary place. The monsters are out there. But that’s why we’re here. We all became cybersecurity professionals to fight for a better world; to protect our organizations, our families, and our future. Now let’s get out there and fight.
Recent Comments