Wanting to Stream the Italian Grand Prix This Weekend? It Might Be a Scam.
With so many fans worldwide wanting to watch the race online, cybercriminals have stepped up to meet the demand with fraudulent websites intent on stealing credit card details.
So you want to catch some or all of the Formula One race this weekend and do a search on the web for “Italian Grand Prix Streaming”. U.S. residents can find it on NBC’s sports website, while others can find plenty of articles talking about websites streaming for free.
But be careful!
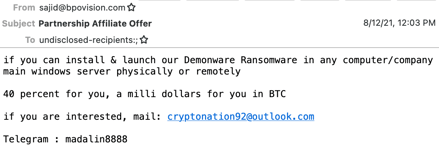
Security vendor Kaspersky analyzed a number of sites claiming to offer “free” streaming, only to be asked to pay a small fee of $1 USD. While it seems inexpensive enough, it’s not the $1 the site owners want… it’s your credit card details. In other instances, phishing websites are setup to steal online credentials.
No matter the particular scam, cybercriminals are keen to take advantage of any heightened sense of need (in this case, to watch something you can’t easily do for free) as the hook for providing scammers with valuable details they can use or sell.
These kinds of scams are generally targeting individuals rather than corporations, but it’s just as easy for cybercriminals to target those wanting to watch a sporting event that occurs during business hours. And, instead of stealing credit card data, they use a simple “install our streaming viewer app” which turns out to be malware.
Keep your employees vigilant against such scams – whether they are at home or work – through continual Security Awareness Training, educating them on current scams, methods, techniques, and themes so phishing attacks that occur via email or the web can be easily spotted before it’s too late.
Recent Comments