Egress: 73% of Orgs Were Victims of Phishing Attacks in the Last Year
A survey sponsored by Egress found that 94% of organizations suffered insider data breaches over the past year. The survey offers the following results:
- “94% of organisations have experienced an insider data breach in the last 12 months
- “Human error is the leading cause of serious insider data breaches, with 84% of organisations experiencing a security incident caused by a mistake
- “However, malicious insiders are IT leaders’ biggest worry, with 28% indicating that it’s their top concern
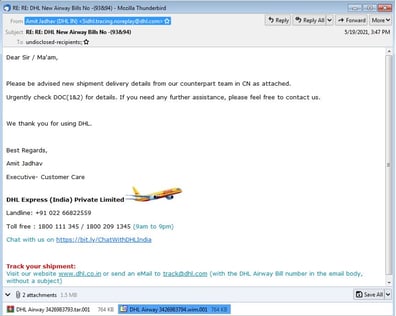
- “Almost three-quarters (74%) of organisations have been breached because of employees breaking security rules, and 73% have suffered serious breaches caused by phishing
- “97% of employees say they would report a breach – which is good news for the 55% of IT leaders who rely on employees to alert them to incidents
- “But it’s not necessarily positive when they do: 89% of incidents led to repercussions for the employees involved
- “Over half (56%) IT leaders believe that remote/hybrid working will make it harder to prevent data breaches caused by human error or phishing
- “By contrast, 61% of employees believe they are less, or equally as likely, to cause a breach when working from home”
Egress notes that organizations should be careful about punishing their employees for these incidents after the employees report their errors.
“The research revealed that an overwhelming 97% of employees would report an insider data breach to their employer – which is reassuring for the 55% of IT leaders who rely primarily on employees to report incidents,” Egress says. “However, when employees do speak up about breaches, it can cost them: the research found that 89% of incidents lead to repercussions for the employees involved, including informal and formal warnings, and dismissal. In addition, just 54% of employees said that they feel their organisation’s security culture trusts and empowers them, indicating that many organisations lack a security-positive culture.”
New-school security awareness training can create a culture of security within your organization by teaching your employees to follow security best practices.
Recent Comments