It’s the start of tax season. This is the time of year when we collect our receipts and tax forms and hope for a nice big refund from the U.S. government. Unfortunately, cybercriminals are also looking for a nice big score as well. This year is going to be worse than ever, as many people have been struggling to make ends meet during the pandemic and are really looking forward to that refund.
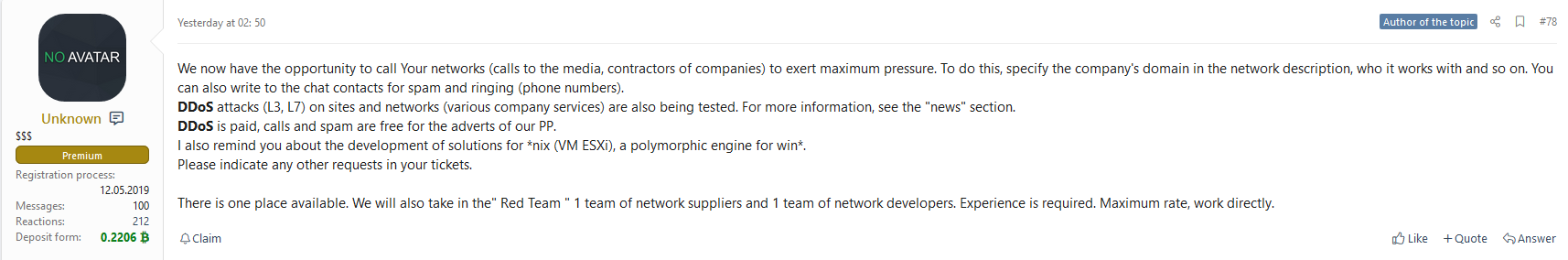
According to an article by Bleeping Computer, taxpayers are being targeted with phishing attacks with RAT malware that is more aggressive than ever before. And with the new extended deadline, this only means these cybercriminals will use every social engineering technique in the book. As unemployment has skyrocketed and people have found themselves struggling to pay the bills, the pressure is on and many will look to their potential tax refund for some relief. This is going to open the door for scammers and cybercriminals to practice their craft.
Don’t Let Your Emotions Get The Best of You
Two of the most powerful tools in the scammer’s toolbox are fear and anxiety. These emotions push people’s brains into a mode of thinking closest to their animal instincts. This is known as System 1 thinking, the automatic and fast way that humans make decisions. While this method of thinking is very handy when helping us avoid a soccer ball kicked at us, it interferes with our ability to make rational decisions. By exploiting our emotions, the attackers can improve their chance that victims will overlook important gaps in the stories they are using against them. Due to COVID-19 and the anxiety already being felt, this year will be worse than ever when it comes to tax scams.
Tax scams are nothing new. They have been happening for decades. Some cybercriminals target the tax forms of the employees of entire organizations, while others target individuals for sensitive personal information and bank account information.
Same Old Attack, New Approach
W-2 scams have varied in popularity over the last few years, but never truly die off. In these scams, the attacker typically contacts the target, often a member of the HR staff, through a phishing email. The contact is made to look like it came from an executive and has requested the W-2s of all of the employees for some sort of tax reason. There is usually a story that makes the request seem urgent and a request to just attach them to an email reply. The email address they reply to with the attachment is not the executive, but the scammer. This year, I expect many of the stories behind the urgency to be COVID-19 related. I suspect we will see tales about the IRS being behind in processing so they need to file taxes early, or that some COVID-19 related tax break or credit is due to expire and they will miss it if they do not get the taxes done immediately. Once acquired, attackers will either sell the information from the tax forms or will attempt to file taxes on a victim’s behalf, claiming a significant refund, using the information on the W-2s. Then when the legitimate person tries to file his/her taxes, he/she is told it has already been done. This can take a year or more to sort out with the IRS and is very unpleasant. Organizations need to be aware of, and be prepared for, these attacks in order to protect their employees.
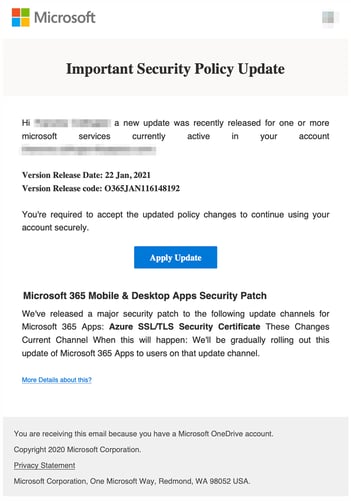
Another common scam around this time of year is the request to ‘verify’ a bank account. The victim will receive an email or text message pretending to be from the IRS or their bank, and will ask them to verify their account information, usually through an included link. They are often told their refund will not be deposited unless they take this step. This link will lead to a fake login page where the individual will enter their login information to ‘verify’ the account. This really just sends their login information to the cybercriminals, who then use it to access the account themselves.
Always Think Before You Click!
These are just a couple of the scams we can expect to see in the midst of heightened tensions and feelings of desperation caused by the pandemic. The best defense against these is information. It is important to teach people how to identify how the scams work so they can spot the signs regardless of the story being used. People should be taught that when confronted with an email, text message or even a phone call that causes a strong emotional response, it should be a warning sign that alerts them to be suspicious. In addition, if sensitive information of any kind is being requested, the recipient should attempt to confirm the request through a Google search (e.g., “IRS email to verify bank accounts”), or in the case of executive requests, verify the request with them over the phone on a known, good phone number.
Many of us are tired, stressed and dealing with situations we never dreamed possible two years ago. However, we need to stay vigilant against attackers that are using this to their advantage before May 17th. If we don’t, we are likely to add more stress to our lives when the attackers win with their social engineering tactics.
Recent Comments