Confident About Detecting Spoofed, Scam Emails?
A survey by ESET found that most people think they’d be able to identify scam emails while shopping online. 87% of respondents said they felt secure while shopping online, while 73% believed they would be able to spot a phishing email impersonating an online retailer. Only 38%, however, said they felt “very secure” online. Unsurprisingly, the survey found a dramatic increase in online shopping since the onset of the pandemic.
“The ESET Global FinTech Study examined the online shopping and cybersecurity habits of 2,000 consumers in the United States and 8,000 consumers across the UK, Australia, Japan, Mexico and Brazil, and found that 70 percent of Americans are shopping more online than they did before the pandemic, with 36% doing so ‘much more often’ than before,” ESET says. “Forty-four percent said they expected to do more online shopping post-pandemic; however, 17% expect to do less, while 32% say their habits will not change compared to their current ones.”
Tony Anscombe, ESET’s chief security evangelist, said that people can be expected to continue shopping online more often even after the pandemic subsides.
“Our lives were becoming increasingly digitized even before COVID-19 hit and now, as we begin to enter a new phase of the pandemic, consumers will likely maintain much of the online habits they became used to during the lockdown, particularly shopping online,” Anscombe said. “With this continued reliability on using the internet for many of our daily routines, it is imperative that the devices and technologies we use to share our most sensitive information are protected to the highest standard and that people understand how to protect themselves.”
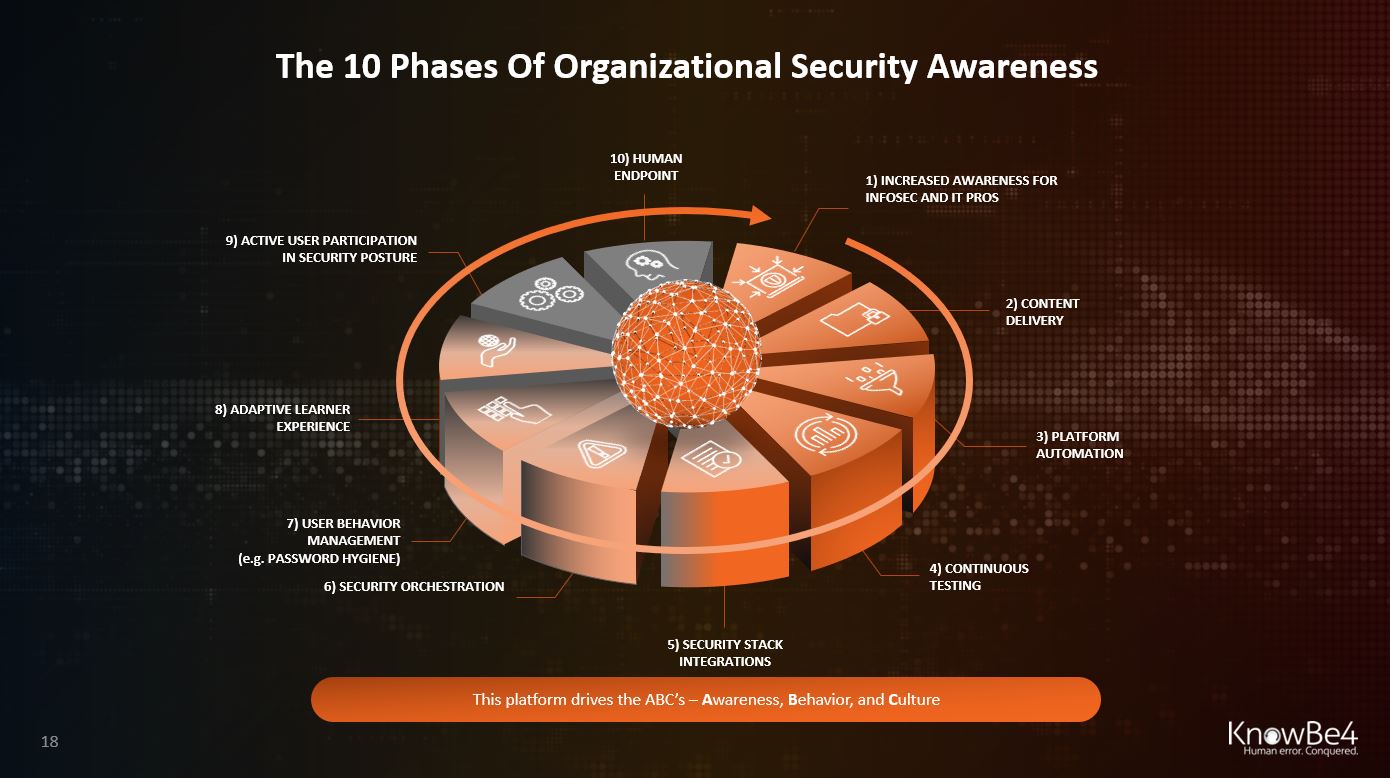
Confidence is fine, we suppose, but overconfidence? Not so much. As phishing emails grow more realistic and harder to distinguish from the real thing, it’s important not to grow complacent about your ability to spot these schemes. New-school security awareness training with simulated phishing tests can teach your employees to identify social engineering attacks in their personal and professional lives.
 Here’s how it works:
Here’s how it works: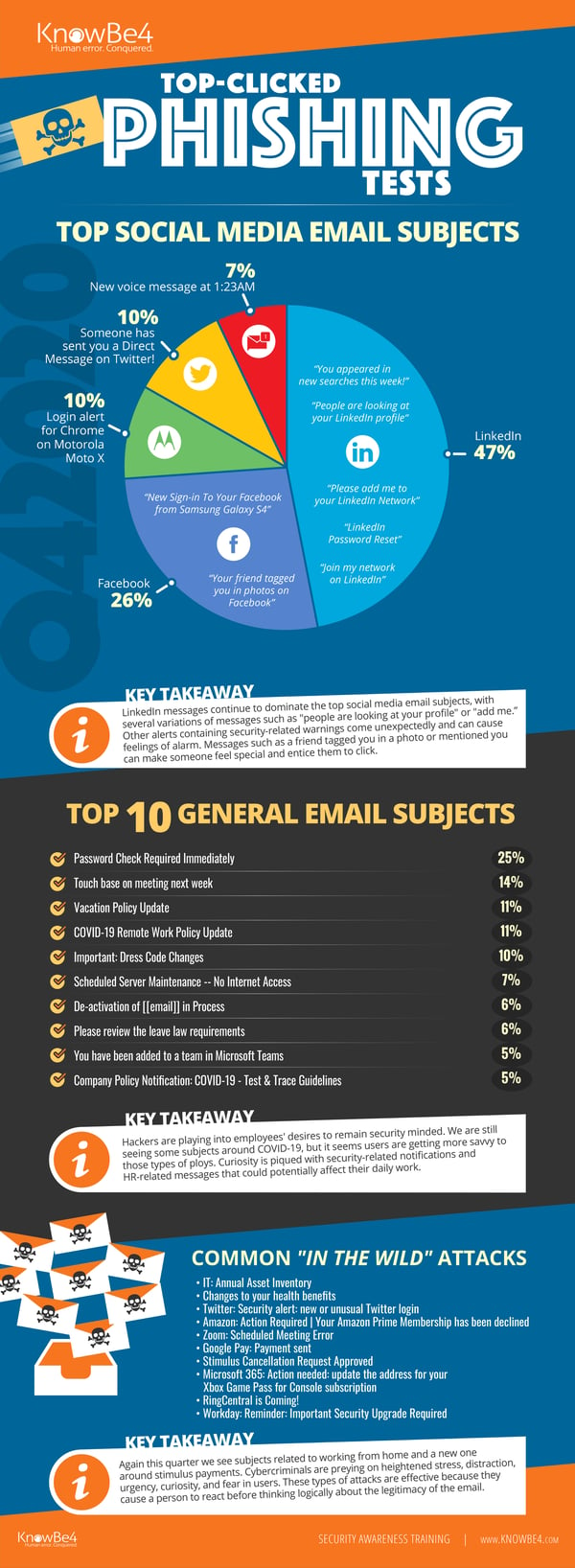
Recent Comments