Travel-Themed Phishing Attacks Lure Victims with Promises of Free Tickets, Points, and Exclusive Deals
New analysis of December and January emails shows massive spikes in attacks aimed at stealing personal information and credit cards under the guise of once-in-a-lifetime travel deals.
Who wouldn’t want a free airline ticket, or a ton of frequent flyer points in exchange for little-to-no effort? That’s exactly the sentiment attackers are going for, according to new analysis by email security vendor BitDefender’s Antispam Lab. Nearly 10% of all spam was travel themed within the timeframe of December 20th through January 10th, with a little more than half (53%) of it targeting the United States.
Many of these scams focus on credential theft. According to the findings, travel rewards programs and gift cards are the most often used subjects, as the personal details held within those programs include birthdates, social security numbers, etc. that can be monetized by selling them on the dark web.
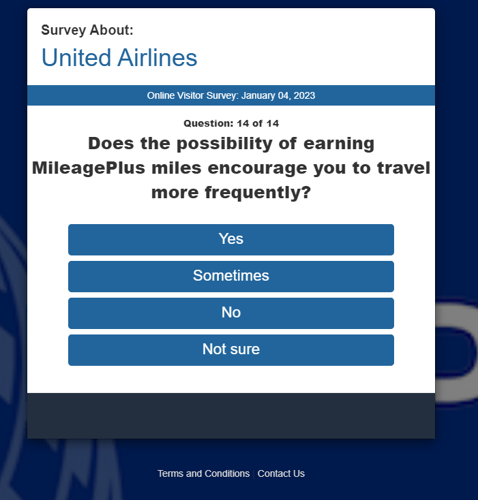
BitDefender offered up a few examples of these emails – notice how legitimate they look:
Source: BitDefender

Source: BitDefender
As we see travel return to pre-pandemic levels, mixed with an increase in fuel surcharges and flight prices, the opportunity to trick someone with the “too good to be true” deal is alive and well with scammers.
Recent Comments