With the holiday season now in sight, businesses and consumers alike have begun to prepare for the annual shopping and gift giving frenzy. Prices are seeing a much-needed plunge, but this is also the time of year where cybersecurity hygiene tends to drop, too.
As inboxes flood with messages about markdowns galore, opportunistic cyber criminals use this time to step up their holiday scams. This post covers why seasonal retail is under attack by cyber criminals, five common holiday season scams, and what businesses and shoppers can do to keep up their cyber defenses.

Why Seasonal Retail Is Under Attack
From late November through to the end of the year, consumers across the globe rack up billions of dollars shopping holiday deals and giving generously to charities. When the COVID-19 pandemic first impacted the world in early 2020, online shopping surged, and now more people than ever make purchases virtually.
Deloitte’s 2022 Holiday Retail Survey found that the online shopping trends seen during the pandemic have endured. This year, the survey reported that online shopping took a 63% share, which is on par with the previous two years.
Shoppers this year also note they are not “giving up the convenience of online shopping” even as they warm up to in-store visits, and 66% of retail executives expect online holiday shopping traffic to have at least single-digit growth over last year.
Those figures are naturally attractive to cyber threat actors, who hope that the dash to grab the best discounts on items with limited availability will lead buyers to fall for fraudulent activity.
Scammers take advantage of unsuspecting shoppers in multiple ways, including through fake websites, discount campaigns, and even charities, to obtain personal and financial information.
Here are five ways threat actors take advantage of the holiday season and how consumers and businesses can stay protected.
1. Fake Ads and Malicious Links
This is the time of year when scammers zero in on targets who are searching for the best markdowns and bundle promotions, trying to spread their dollars further. Scammers run fake ads showing valuable and hard-to-get items at incredible prices. To encourage shoppers to click, they often use urgent phrasing, promising attractive discounts only while supplies last, or for a limited time only.
To further increase clickability, scammers use the same marketing strategies as legitimate ads to trick shoppers who are already moving faster than usual and may have their guard down. Once an unsuspecting victim clicks the link, they are led to fraudulent sale sites with credit card skimmers embedded in the code.
How To Stay Safe:
- Shoppers can protect themselves from fake ads and malicious links by performing a quick check on the product being advertised. See a deal too good to be true? Pull up the official website of the brand and check if the same sale prices are reflected on their product pages.
- Don’t rely on the quality of the photos displayed in the ad. Pixelated images can be an immediate red flag, but scammers also rip off genuine photos from official brand websites.
- If a sale site seems sketchy, check for inconsistencies in spelling and language. Confirm that the website includes comprehensive policies on shipping, returns, customer support, and privacy. A privacy policy should cover how the company collects, uses, and protects personal and transactional data.
- Check if the site is trusted by looking for “https” at the beginning of the site’s URL and ensure there is a closed lock or unbroken key icon. These icons indicate that data submitted on the site is encrypted.
2. Fake Discounts & Coupon Code Apps
Scammers will go to great lengths to obtain sensitive information. Other than hosting fake ads with bad links, they also build fraudulent applications that claim to search for and consolidate discount codes and coupons from popular brand names.
These fake apps are usually distributed through unofficial app repositories with the intention of having users download malware onto their devices, stealing payment information, or credentials to social media or online banking accounts.
How To Stay Safe:
- If a company name seems unfamiliar, check for community reviews and how long the app has been around. Scam apps are typically less than a few months old.
- Shoppers should look up the details of the app’s developer. How easy is it to find out the developer’s identity? If it’s not obvious who they are and where they trade from, walk away.
- Use a security product to check if the application is known malware, or use public malware checking sites like VirustTotal to check an application or suspicious file’s reputation (be careful not to upload personal files – anything uploaded there is shared publicly!)
3. Holiday Email Scams & Phishing Campaigns
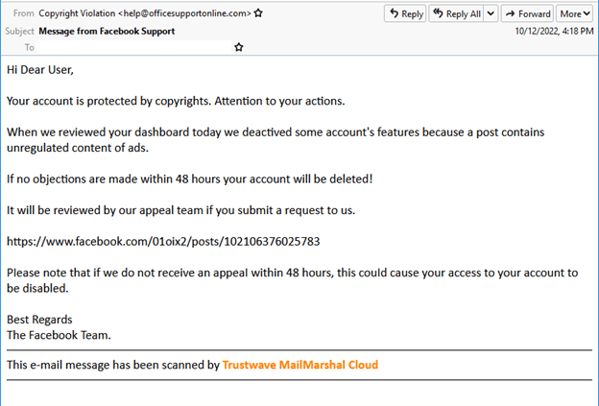
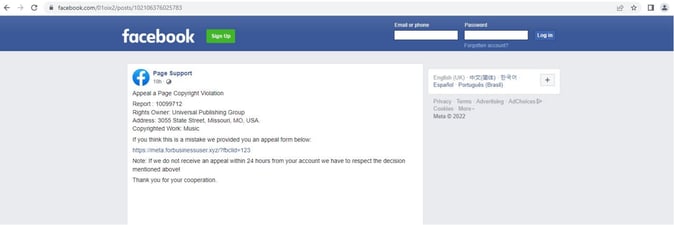
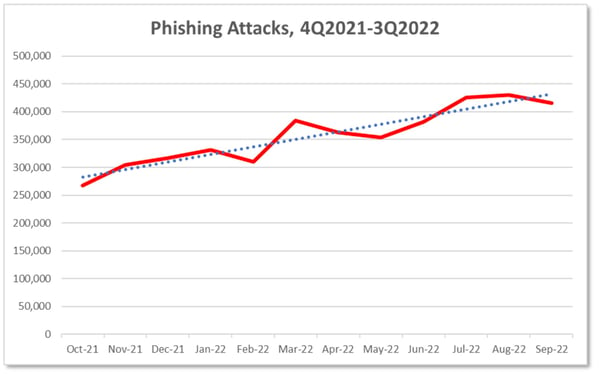
Sometimes all it takes is an unassuming email and a clever subject line to sink the hook. The holiday season is rife with phishing scams as cyber threats actors take to hiding amongst the throngs of legitimate emails from big brands.
Some scammers create spoofs of legitimate holiday emails from established brands and lure in their target with bargain prices. Clicking the links leads shoppers to malicious websites primed to drop malware or phish for login credentials.
Other than offering special gifts, bundle pricing, and extra coupons, holiday email scams may also send shoppers invoices for items they did not purchase. These kinds of emails include deceptive links to “report a problem” or reach a customer service team member. The scammers hope that indignant shoppers will fall for the links and click, thinking they can dispute the invoice.
How To Stay Safe:
- Defend against social engineering scams by using trusted security software to block out malware.
- Make sure your device operating system is up-to-date and your accounts are protected by Multi-factor authentication.
- When reading emails, inspect link addresses before clicking on them. Scammers often use URLs that look similar to real ones, replacing letters and spacing with numbers and punctuation or using odd domains.
- Shoppers can also check that their browser settings are set to show full website addresses by default and that the appropriate privacy and security settings are all turned on.
4. Fake Charity Sites & Scams
The winter holidays is often a time of paying back one’s gratitude through charity and threat actors are waiting on the side lines to exploit the season’s givings. Scammers will often take full advantage of people’s generosity during this time of year by spoofing the phone numbers of legitimate charities and impersonating the agents to ask for donations.
Some cyber scammers may send text messages, target people through social media, or set up a computerized auto dialer to deliver pre-recorded messages.
How To Stay Safe:
- Be wary of these solicitations whether online, via phone, or even in person. The safest way to donate to a charitable organization is to reach out to them proactively, or simply donate through their official website.
- Check that the websites have firm payment protection in place and always use a credit card rather than providing direct account information.
5. Fake Offers for Seasonal Work
Businesses often hire in advance of the busy holiday season. Consumers who have trusted known brands for years may find themselves applying for a little part-time, seasonal work only to find that they’ve given away personal information to a fraudster.
Scammers in these schemes impersonate HR representatives, recruiters, and even senior managers of real companies and post help-wanted ads via email or on social media platforms.
Usually, these open roles will include forms for the hopeful applicant to fill out and ask for intimate details such as address, tax details, social security number, work permit information, and other personally identifiable information (PII).
If the ad is not directly phishing for PII, then applicants may be led to bogus sites that scan for email addresses and passwords or even ask them to pay upfront for job supplies and training fees.
How To Stay Safe:
- Holiday job seekers should research the company, review their website and associated channels. Check their Careers landing page to find the official job posting and ensure that the details of the role are the same.
- Remain cautious of roles that have vague job requirements, pay an unusually high wage, or promise applicants that they will “make money fast”. Receiving a job offer right away after applying and without an interview is another common red flag.
- Only give personal information directly related to the application process after you have met in person or over video with a member of the company’s HR department.
Cybersecurity Is Crucial For the Holidays
We’ve covered many common scams that day to day consumers face during the holiday rush, but it’s important for businesses to protect themselves and their customers from cyber threats, too. During the holiday season when threat actors are more active, businesses may equally find that they are understaffed and dealing with heavy demand.
During the holiday season, businesses should be prepared to see increases in malware campaigns, ransomware and data extortion, Distributed-Denial-of-Service (DDoS) attacks, and the possibility of data loss.
As the number of digital transactions soars during the holiday season, establishing better cybersecurity processes can help to keep businesses and their customers safe from holiday scams.
- Establish Full Visibility & Managed Security – Consumers often favor online shopping because of the convenience of shopping 24/7. This means that malicious activity can happen at any hour of the day, even outside the business hours of a company’s IT team. Having round-the-clock protection is crucial to identifying malicious behavior in its earliest stages before lateral spread can occur.
- Execute Pre-Seasonal Audits – Before the holiday rush, companies should perform thorough security checks to validate any recent coding changes, SaaS updates, and third-party code on payment pages especially. Check that sensitive areas of a network are adequately protected and minimize the exposure of critical data and assets.
- Ensure & Maintain Compliance Controls – Businesses that collect payment through credit cards must be in compliance with the requirements of the Payment Card Industry Security Standards Council (PCI CSS). The council focuses its controls on protecting payment account security during digital transactions. Retail companies accepting, processing, storing, or transmitting credit card information and cardholder data must meet controls set out in the Payment Card Industry Data Security Standard (PCI DSS) framework.

Recent Comments